Getting Started
Purpose and audience
This document is intended for security, cloud, DevOps, and IT operations teams using Saner CNAPP to gain unified visibility across cloud environments like AWS, Azure, GCP and identify misconfigurations and vulnerabilities, prioritize risks, and drive remediation. It focuses on day-to-day operational best practices for securing cloud infrastructure, resources and identities, rather than just initial setup.
How to use this guide
Use the sections for a first-time CNAPP rollout, then adopt them as part of your ongoing cloud security operations. Each section includes practical actions, recommended cadences, and reporting guidance to enable continuously identify, prioritize, and remediate risks across cloud environments with minimal manual effort.
Prerequisites
- Access to the Saner CNAPP console with appropriate roles (view, scan, remediate, and report).
- Cloud account onboarding completed with required permissions (read-only for discovery and additional permissions for remediation where applicable) across supported platforms (e.g., AWS, Azure, GCP).
- Proper IAM role and access configuration to enable secure integration between Saner and cloud environments.
- Notification channels (email, ticketing or chat) configured for alerts and reports.
- A simple ownership model for remediation: who triages, who fixes, who approves exceptions, and who validates closure.
Glossary
- CNAPP: Cloud Native Application Protection Platform.
- CCHS: Cloud Cyber Hygiene Score.
- CSAE: Cloud Security Asset Exposure module.
- CSPM: Cloud Security Posture Management module.
- CIEM: Cloud Infrastructure Entitlement module
- CSPA: Cloud Security Posture Anomaly module.
- CSRP: Cloud Security Risk Prioritization module.
- CSRM: Cloud Security Remediation Management module.
Saner Cloud Native Application Protection Platform (CNAPP) Best Practices
Saner Cloud-Native Application Protection Platform (CNAPP) provides unified capabilities to discover cloud resources, identify misconfigurations, and identity risks, prioritize security issues, and remediate them through automated and guided actions, all from a single centralized console.
In this document, let us discuss the best practices in Saner CNAPP to help you maximize visibility, strengthen cloud security posture, and effectively reduce risk across your cloud environments.
Measuring and Maintaining Cloud Cyber Hygiene
It is critical to quantify the security posture risk of your cloud environments, as it provides multiple advantages. From having a baseline on which you can see the impact of your security measures, a hygiene score can also help you communicate risk with the management. Here’s how you can make the best use of Saner’s Cloud Cyber Hygiene Score (CCHS).
- Use the CCHS dashboard to track cloud cyber hygiene trends across accounts, subscriptions, and projects. Treat 80 as a practical benchmark for production environments but focus on consistent improvement and stability rather than targeting a single number. Regularly review the key contributors to the score, such as misconfigurations, identity risks, anomalous activities, and exposed resources, and validate improvements using trend views.
- Leverage the CCHS trend dashboard to monitor the effectiveness of your remediation efforts over time. For deeper insights, refer to account-level and resource-level views to identify high-risk environments and prioritize remediation based on severity and service impact.
Gaining Visibility Over Cloud Asset Exposure
Saner CNAPP’s Cloud Security Asset Exposure (CSAE) module provides continuous and real-time visibility into your cloud environment. With Saner, you can discover and monitor cloud resources such as compute instances, storage services, databases, serverless functions, and networking components across multiple accounts and regions. It helps identify publicly exposed resources, shadow assets, and misconfigured services that may increase your attack surface. The following are the best practices to gain complete visibility and control over your cloud assets.
- The first step in securing your cloud environment is to establish complete visibility across all resources. Activate continuous discovery to identify assets spanning accounts, projects, and regions. Conduct regular monitoring to detect newly created, publicly accessible, outdated, or unassigned resources. Act promptly by applying unique tags and organizing resources into logical groups across all Saner CNAPP modules.
This process delivers clear visibility into the inventory of deployed cloud assets, enabling better understanding of resource distribution and helping to identify redundant or unnecessary resources.
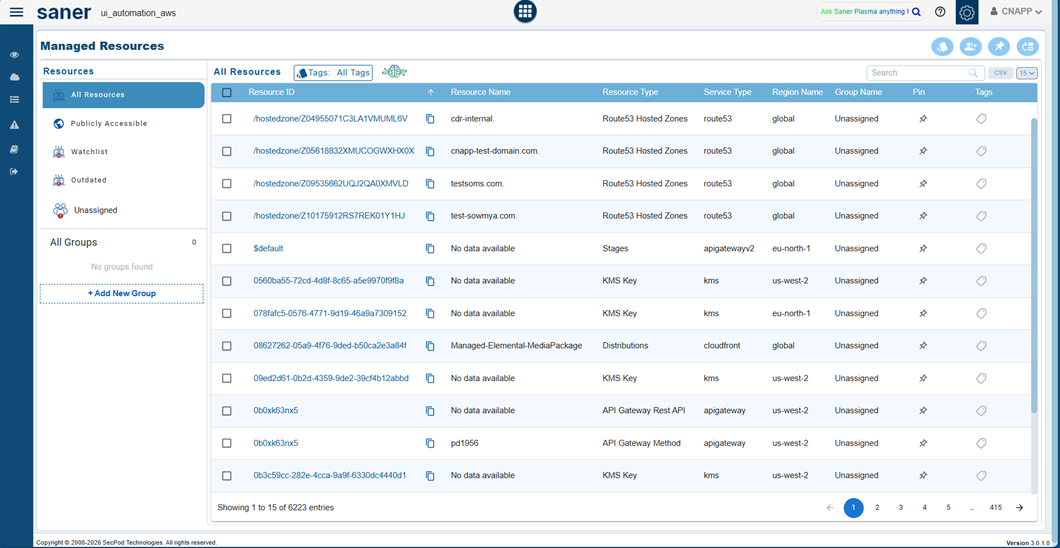
- Exposed and misconfigured cloud resources pose significant security risks. Use Saner’s aggregated resources view to identify publicly accessible resources, high-risk configurations, and shadow resources. Prioritize and remediate these risks using CSRP and CSRM respectively and leverage the Watchlist feature to continuously monitor critical cloud services across AWS, Azure, and GCP for improved visibility and faster response.
Outdated or deprecated cloud resources can introduce security risks, compatibility issues, and unnecessary costs. Using Saner, identify such resources from the saner CNAPP dashboard and take appropriate actions such as upgrading, replacing, or deleting them to maintain a secure and optimized cloud environment.
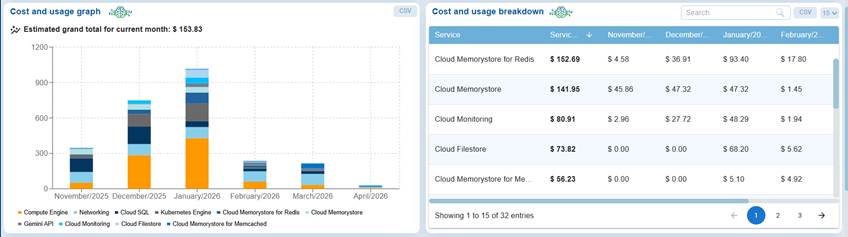
- Unused or misconfigured cloud resources can lead to unnecessary costs and inefficient resource utilization. Use Saner’s cost and usage dashboard to monitor spending across services, identify high-cost or underutilized resources, and take appropriate actions such as rightsizing, optimizing, or decommissioning them to improve cost efficiency and maintain a secure cloud environment.
In the left-hand panel, cloud alerts to get instantly notified of newly created resources, outdated resources, watchlisted resources, and publicly accessible resources. This helps you stay on top of any changes in your cloud security asset exposure and respond to risks proactively.
- Automate weekly Cloud Asset report and configure them to your mailbox and assess your organization’s vulnerability posture regularly. To configure the report to your mailbox, Select the email icon from the right-hand side and specify the email address to view the report.
Detecting and Managing Anomalous Deviations
A key differentiator of Saner CNAPP is that it can detect and manage posture anomalies in users’ cloud infrastructure to provide broad security coverage from potential risks that other scanners don’t even recognize. With Saner CNAPP’s Posture Anomaly Management module, users can achieve comprehensive security coverage and ensure that no risks can be exploited by hackers.
Common posture anomaly examples to operationalize early:
- Publicly accessible storage resources (e.g., open buckets or blobs) without proper access restrictions.
- Excessive IAM permissions or privilege escalations beyond defined policies.
- Unusual or unexpected exposure of services such as open ports or unrestricted network access.
- Misconfigured security groups, firewall rules, or network policies allowing broad access.
- Resources deployed outside approved regions or without proper tagging and governance controls.
- Inactive or orphaned resources that may still be accessible and pose security risks.
Here’s how you can best use the posture anomaly management module:
- With Saner CNAPP, posture anomalies are detected as part of the unified full scan across your cloud environment. These scans run continuously to provide up-to-date visibility into misconfigurations, identity risks, and anomalous behaviors. Ensure that regular scans are enabled and aligned with your organization’s requirements to maintain continuous monitoring and quickly identify deviations in your cloud security posture.
- Beyond just detecting these anomalies, it is critical to fix them too. In Saner, you can fix anomalous posture with built-in remediation, with an array of built-in actions. You can also create your own detection rules to identify the anomalies and remediate them instantly from the same console to secure your IT environment. In the Posture Anomaly dashboard, you can click on the wrench icon and follow the instructions based on the pop-up. The controls can also be implemented through other modules, namely Endpoint Management.
- Some posture anomalies might not be a risk for your organization’s setup and environment, so you whitelist them as necessary to make it known-good. This step will ensure that it is not detected as a potential risk in the next scan. Here’s how to do it. In the PA dashboard, you can click on the whitelist button on the menu bar and go to the whitelist page. On the page, you can select the anomaly rules that you want to whitelist and click on save. These steps will whitelist the controls, and they won’t show up in the next scan results.
- Examine your security posture with an insightful dashboard and reports. These dashboards and reports help you get a better understanding of the risk your network might be in and ensure you take action on these risks. Here’s how you can generate the reports: Click the Reports button on the left side menu bar, click on Saved Reports, and select Posture Anomaly Report to get a comprehensive report of the account.
Prioritizing Security Risks (CSRP)
Scanning for security risks is just the 1st step of the misconfiguration management process. But when the number of detected vulnerabilities are in millions, it is critical to prioritize risks to maximize the attack surface reduction and improve the efficiency of the IT Security teams. With Saner Cloud’s Risk Prioritization module, this process becomes significantly easier. Here are some best practices to prioritize security risks effectively with Saner Cloud.
- It is always suggested to categorize risks based on criticality and other metrics to prioritize risks effectively. When choosing which vulnerability to remediate first, Saner Cloud simplifies the process by categorizing risks into ACT, ATTEND, TRACK, and TRACK* to help users focus on which security risk to remediate first.
Recommended actions for each bucket (adjust SLAs to your operating model):
- TRACK*: Track as an exception. Document the business reason, compensating controls, and a review date.
- TRACK: Monitor and mitigate for lower-risk findings or items awaiting fixes. Reasses periodically based on risk changes.
- ATTEND: Plan and remediate soon for high-impact items that need coordination or testing. Suggested SLA: 7-14 days.
- ACT: Remediate immediately for exploitable, internet-facing, or business-critical assets. Suggested SLA: 24-72 hours.
- Remediating risks should be closely tied to risk prioritization. It becomes simple and routine with Saner to remediate risks with a click of a button. By selecting risks that are already categorized based on priority, you can just click on the wrench icon for remediating and mitigating the security risks.
- You can also leverage MITRE ATT&CK Mapping to understand the prioritization logic and sort based on criticality in the MITRE ATT&CK Mapping tab in the top menu. Once clicked, you can also select and remediate risks with integrated remediation.

- Examine your prioritized security risks through insightful dashboards and reports. These dashboards provide a clear understanding of risk distribution across your cloud environments and help you take action based on priority. To generate the reports, click the Reports button on the left side menu bar, navigate to Saved Reports, and select the Risk Prioritization Report to get a comprehensive view of categorized risks across your accounts.
- In the left-hand panel, configure alerts to get instantly notified of critical and high-priority risks identified by CSRP. This helps you stay on top of ACT and ATTEND category risks and enables faster response to high-impact security issues across your cloud environments.
Remediating Security Risks (CSRM)
Remediation plays a critical role in reducing cloud security risks and minimizing the attack surface. Saner Cloud Security Remediation Management (CSRM) enables you to remediate misconfigurations, identity risks, exposed resources, and vulnerabilities through guided and automated actions. The following best practices will help you remediate risks efficiently and strengthen your cloud security posture.
- Remediation plays a critical role in reducing cloud security risks and minimizing the attack surface. Saner Cloud Security Remediation Management (CSRM) enables you to remediate misconfigurations, identity risks, exposed resources, and vulnerabilities through guided and automated actions across CSPM, CIEM and CSPA. The following best practices will help you remediate risks efficiently and strengthen your cloud security posture.
- Predefined remediation actions help you efficiently fix misconfigurations and security risks across your cloud resources. In Saner, navigate to the respective module (CSPM, CIEM, or CSPA) to view a list of available remediations. Select the required remediation actions based on severity and affected services and apply them to enforce secure configurations across your cloud environment.
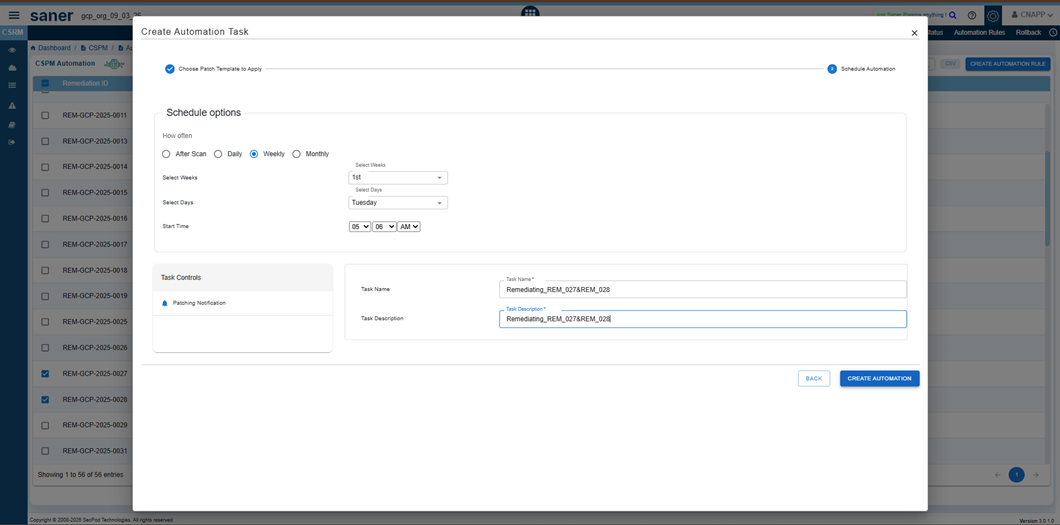
- Scheduling remediation tasks helps ensure controlled and non-disruptive execution across cloud resources. While creating a remediation task in Saner Cloud, define the task details, select the required resources and remediation actions, and configure the execution schedule by specifying the date and time. This allows you to plan remediation activities during a suitable schedule and minimize potential impact on running services.
- Manual remediation of cloud misconfigurations can be time-consuming. In Saner CNAPP, navigate to CSRM → select any module(CSPM, CSPA and CIEM) → Automation Rules, select the required remediation rules, and click on Create Automation Rule to automate remediation actions. This ensures that identified misconfigurations are automatically fixed, helping maintain a secure cloud posture continuously. Regularly monitor the automation results and validate that risks are effectively remediated across your cloud resources.
- If a remediation action leads to unintended configuration changes, use the built-in Rollback option in CSRM (where available) to revert the resource to its previous known-good state. Before applying rollback across multiple resources, validate the impact on a limited set of resources, capture the outcome, and plan a follow-up remediation approach to ensure the risk is addressed without affecting stability.
- In the left-hand panel, Set alerts to get instantly notified when any critical or important remediations are detected and if any remediation job fails.
- In the left-hand panel, navigate to reports, and from the saved reports, Automate the weekly cloud patch report and configure it to your mailbox and assess the success rate of remediations in your organization. To configure the report to your mailbox, Select the email icon from the right-hand side and specify the email address to view the report.
- Measure the impact of patching and view the patches in users cloud infrastructure through an insightful cloud patch management report in Saner. You can access this report through saved reports in Saner.
Hardening Cloud Configurations & Achieving Compliance (CSPM)
Saner CNAPP enables continuous monitoring of cloud configurations to detect misconfigurations, policy violations, and compliance drifts across multi-cloud environments. It helps organizations align with industry-standard compliance frameworks such as CIS, NIST, PCI DSS, SOC 2, and HIPAA, while also allowing the use of SecPod default benchmarks. With continuous posture assessment and remediation capabilities, Saner ensures that cloud resources remain secure and compliant at all times.
- Organizations often operate across multiple cloud providers such as AWS, Azure, and GCP. To ensure consistent security posture, leverage the predefined compliance benchmarks available in Saner for each cloud platform. Apply relevant benchmarks such as CIS Foundations Benchmarks (AWS, Azure, GCP), NIST SP 800-53 Rev. 5, PCI DSS, SOC 2, and HIPAA HITRUST, along with SecPod default benchmarks, across your cloud accounts. This helps standardize configuration policies, continuously monitor compliance, and quickly identify and remediate misconfigurations across your cloud environment.
- You can select the Create New Benchmark option from the right-hand side and create different benchmark templates.
- If a user needs to fix a compliance deviation, click on the wrench icon corresponding to the Cloud Security Posture Management Rule in the right-hand side.
- In the left-hand panel, Configure Alerts to get instantly notified of any deviations in compliance.
- In the left-hand panel, navigate to reports, and from the saved reports, Automate the weekly compliance report and configure it to your mailbox to assess the compliance posture in your network continuously. To configure the report to your mailbox, Select the email icon from the right-hand side and specify the email address to view the report.
Managing Identities & Enforcing Least Privilege (CIEM)
Not all cloud risks originate from vulnerabilities, many arise from over-permissioned identities, misconfigured roles, and excessive access rights. These risks cannot be remediated through patching and require identity-centric security controls.
Saner CIEM enables organizations to gain visibility and control over cloud entitlements by providing capabilities to:
- Analyse identities, roles, and permission assignments
- Detect excessive or unused privileges
- Identify inactive or orphaned accounts
- Monitor policy misconfigurations and risky access patterns
- Enforce least-privilege access across multi-cloud environments
Best Practices for Identity & Access Governance
- Configure Continuous Entitlement Checks
Set up checks to monitor critical identity and access parameters such as:- Over-privileged users, roles, and service accounts
- Excessive or unused permissions and policies
- Inactive or dormant identities
- Misconfigured IAM policies and role bindings
- High-risk actions and privilege escalation paths
- Unused roles, groups, or applications
- Cross-account or cross-project access exposure
Continuous monitoring helps identify deviations from least-privilege principles and enables timely remediation of identity risks.
Cloud-Specific Focus Areas
- AWS
The platform focuses on analyzing IAM configurations (users, groups), including policies, roles, and permission boundaries, to identify overly broad permissions and inactive identities. It detects misconfigurations such as excessive privileges and inactive roles and provides remediation options directly within the interface. Users can initiate remediation actions by clicking on the wrench icon associated with each finding.
- Critical Activities section provides visibility into user actions by displaying all significant activities performed within the environment. Detailed reasoning for why an activity is considered critical can be accessed by clicking the Evidence icon on the right side of the table.
- In addition, a graphical representation is provided for Users, Groups, Roles, Policies to visualize the relationships between identities, policies, services, and resources. This graph helps illustrate how permissions are granted and highlights potential risk areas, such as excessive privileges or high-risk actions.
- Azure
The platform focuses on analyzing identity and access configurations within Azure, including Microsoft Entra ID users, groups, applications, and RBAC role & Entra role -assignments, to identify excessive permissions and inactive identities. It evaluates access across different scopes, such as tenant, subscription, resource group, and resource level to detect misconfigurations that violate the principle of least privilege. The system identifies risks such as over-privileged role assignments, unused applications, inactive users, and excessive group memberships.
- CIEM also provides remediation option directly within the interface. User can remediate by clicking the wrench icon associated with each finding. Additionally, the Critical Activities section provides visibility into significant actions and activities performed within the Azure environment, including role assignments, application changes, and access modifications. Detailed insights into why an activity is considered critical can be accessed through the Evidence icon on the right side of the Critical Activities table.
- Saner CNAPP also provides a graphical representation of Azure entities including Users, Groups, Applications, RBAC Roles, and Entra Roles along with their assignments. This visualization maps the relationships between identities, role assignments, and resources, making it easier to understand how access is granted across different levels (tenant, subscription, resource group, and resource). It further highlights potential risk areas such as excessive privileges, high-risk role assignments, or over-permissioned applications, enabling proactive remediation and stronger access governance.
- GCP
The platform analyzes Google Cloud IAM configurations, including Users, Groups, Service accounts, Policies and Role Assignments, to identify excessive permissions and potential security risks, which can grant broad access across resources if not properly managed.The system detects misconfigurations such as over-privileged identities, misuse of service accounts, cross-project access, and unnecessary role bindings. It also identifies inactive users and unused service accounts that could pose security risks.
Remediation actions are provided directly within the interface, allowing users to quickly address identified issues, and enforce the principle of least privilege.
- The Critical Activities section provides visibility into operations performed within the Google Cloud environment by analyzing data from Cloud Audit Logs. It captures high-risk actions related to IAM and resource management, such as service account key creation, policy modifications (SetIamPolicy), role assignments, and service enablement activities. Detailed insights into why a specific activity is considered critical can be accessed by clicking the Evidence icon on the right side of the table.
- In addition, a graphical representation is provided for GCP entities such as Users, Groups, Service Accounts, IAM Roles, and Policies to visualize the relationships between identities, role bindings, and resources. This visualization illustrates how access is granted across different levels of the GCP hierarchy, including organization, folder, project, and resource levels.It helps highlight potential risk areas such as excessive privileges, misuse of primitive roles, over-permissioned service accounts, and high-risk IAM role bindings, enabling better visibility into access paths and potential privilege escalation scenarios.
- The left-hand panel provides an option to configure alerts, enabling real-time notifications for any deviations from identity and access compliance policies.
- In the left-hand panel, navigate to reports, and from the saved reports, Automate the weekly compliance report and configure it to your mailbox to assess the compliance posture in your network continuously. To configure the report to your mailbox, Select the email icon from the right-hand side and specify the email address to view the report.
A Checklist of Saner CNAPP’s Best Practice
Use the checklist below as an operational runbook. Add owners, cadence, and evidence links so the checklist doubles as audit-ready proof.
| Module | Checklist item | Owner | Cadence | Evidence or report link | Last run | Notes or exceptions |
|---|---|---|---|---|---|---|
| CSAE(Cloud Security Asset Exposure) | Continuous discovery of cloud resources across accounts, regions, and services | |||||
| Identify publicly exposed resources | ||||||
| Track cost and usage to identify underutilized resources | ||||||
| Configure alerts for new, exposed or high risk resources | ||||||
| Automate CSAE reports | ||||||
| CSPA(Cloud Security Posture Anomaly) | Detect posture anomalies | |||||
| Investigate anomalous configurations and behavior | ||||||
| Whitelist necessary rules to make it known-good | ||||||
| Remediate posture anomalies with the help of wrench icon | ||||||
| Examine security posture with dashboard and reports | ||||||
| CSRP(Cloud Security Risk Prioritization) | Prioritization and Categorization of risks into ACT, ATTEND, TRACK, TRACK* | |||||
| Prioritize risks based on exposure, severity, and impact | ||||||
| MITRE ATT&CK mapping of risks | ||||||
| Remediate high-priority risks (ACT/ATTEND) promptly | ||||||
| Leverage Test & Deploy of patches | ||||||
| Automation rules for automatic remediation management | ||||||
| Rolling back remediations | ||||||
| CSPM(Cloud Security Posture Management) | ||||||
| Enforce compliance and fix misconfigurations with benchmarks | ||||||
| Monitor configuration drifts across cloud environments through scans | ||||||
| Prioritize and remediate high-risk misconfigurations | ||||||
| Alert configuration for immediate notification | ||||||
| Generate audit-ready reports for any compliance policies | ||||||
| CIEM(Cloud Identity Entitlement Management) | Discover all identities with respect to the cloud provider | |||||
| Identify over-privileged and inactive identities | ||||||
| Enforce least privilege across cloud environments | ||||||
| Detect privilege escalation risks and excessive access | ||||||
| Monitor identity usage and anomalous access patterns | ||||||
| Configure alerts for immediate notification |
About SecPod
SecPod builds products that help organizations continuously discover cloud assets, assess security exposure, and reduce risk across multi-cloud environment through prioritized remediation.
The Saner CNAPP platform supports cloud security programs by providing unified capabilities for cloud security asset exposure (CSAE), cloud security posture management (CSPM), cloud infrastructure entitlement management (CIEM), cloud security posture anomaly(CSPA), cloud security risk prioritization(CSRP), CCHS(Cloud Cyber Hygiene Score), and remediation across AWS, Azure, and GCP.
SecPod, Inc.
303 Twin Dolphin Drive, 6th Floor, Redwood City, California 94065, USA.
Contact
Sales : [email protected]
Support: [email protected]
Phone: (+1) 918 625 3023 (US)
To learn more about SecPod, visit: www.secpod.com


