Release Date: 04 Mar 2026
This release introduces support for Google Cloud Platform (GCP) in Saner Cloud, broadening the multi-cloud security coverage to include GCP alongside Amazon Web Services (AWS) and Microsoft Azure.
As one of the leading cloud platforms, GCP continues to see strong adoption, particularly for data analytics, AI, machine learning workloads, and containerized environments powered by Kubernetes. With this GCP update in Saner Cloud, customers benefit from improved visibility, centralized control, and continuous security monitoring across their GCP environments. This enhancement helps to minimize risk and consistently enforce cloud security best practices across multi-cloud infrastructures.
Take a closer look at the updates this release presents:
Complete Visibility into GCP Resources from CSAE
Comprehensive visibility into all GCP cloud resources and their internal configuration details from Saner Cloud Asset Exposure (CSAE) tool dashboard.
Gain centralized visibility across all Google Cloud resources such as Virtual Machine instances (Compute Engine), Cloud Storage buckets, IAM users and service accounts, VPC networks, subnets, Cloud SQL instances, GKE clusters, BigQuery datasets and Load Balancers, Cloud Functions, and Pub/Sub topics, along with their detailed internal configurations as listed below and much more.
- Public exposure settings and external IP assignments
- Network configurations and Encryption settings
- Resource types that are marked for EOL by GCP
- Logging and audit configurations
- Resource distribution by their Services, Resource Categories, and Regions
- Visualize the Cost of resources per month and trend of resource added or removed from GCP infrastructure
- Create watchlists to monitor specific services in target regions

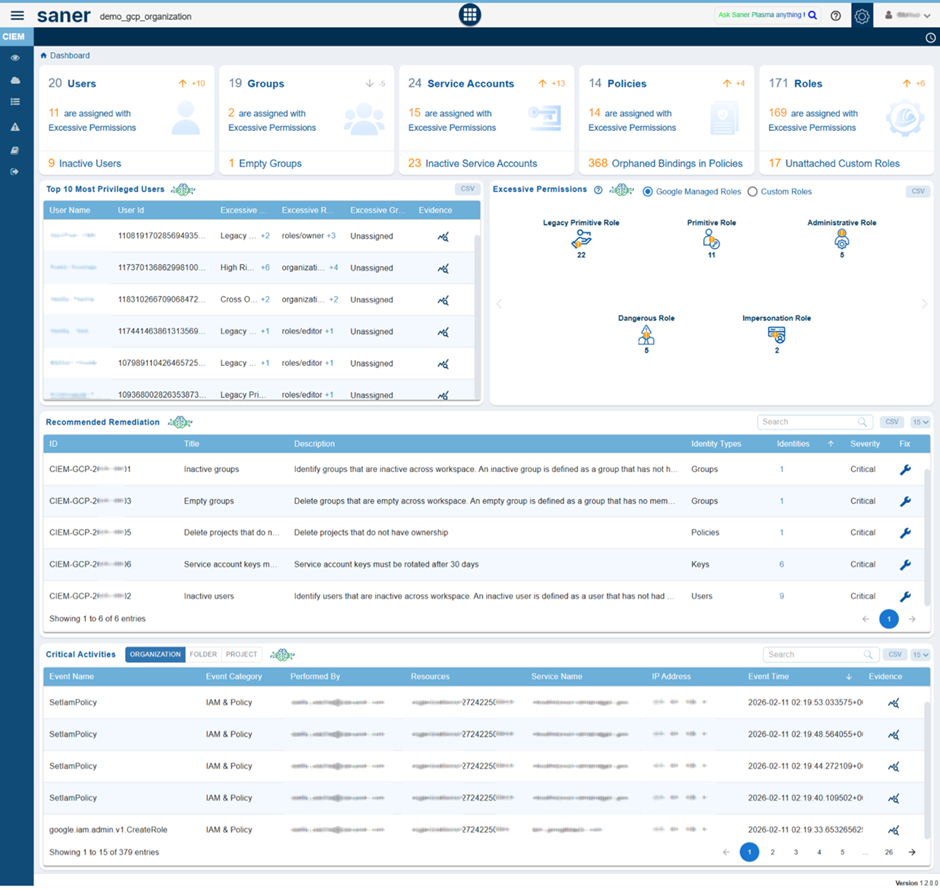
GCP IAM Support In CIEM
Saner Cloud Infrastructure Entitlement Management (CIEM) now includes GCP IAM Security support, enabling centralized visibility and governance of identity and access permissions across Google Cloud environments. This enhancement provides visibility into users, groups, service accounts, policies, and role assignments while enabling detection of excessive permission risks and identification of unused entities to strengthen cloud identity security and governance.
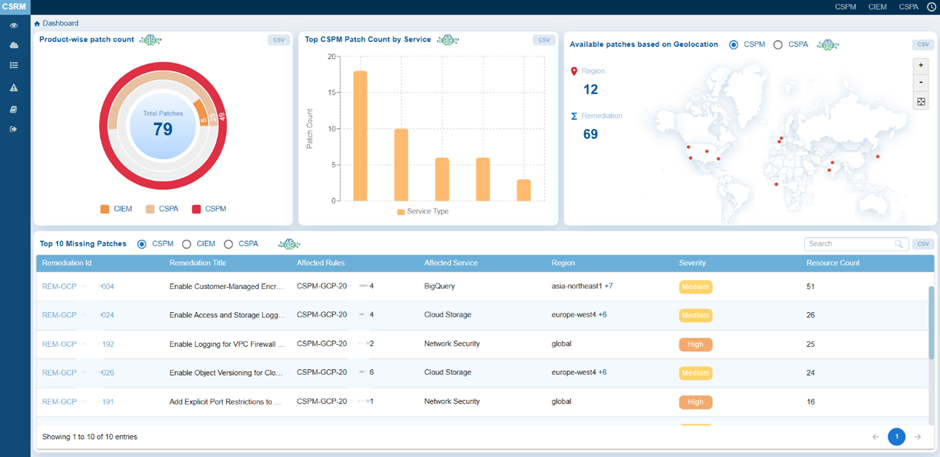
Added Security Checks for Monitoring GCP Benchmark Rules
Saner Cloud Security Posture Management (CSPM) now includes new security checks to continuously monitor GCP benchmark rules and identify configuration deviations. Some of these checks include:
- For Compute Engine Service, check if Block Project-Wide SSH Key is Not Enabled
- Check for Publicly Accessible Cloud Storage Bucket
- Find Cloud SQL Instances without Automated Backup configuration
- In Network Security, look for firewall rule that Allows Unrestricted ICMP Access
This enhancement allows faster detection of misconfigurations and supports one-click remediation through Saner Cloud CSRM (Cloud Security Remediation Management), helping organizations strengthen cloud security posture and streamline remediation workflows.
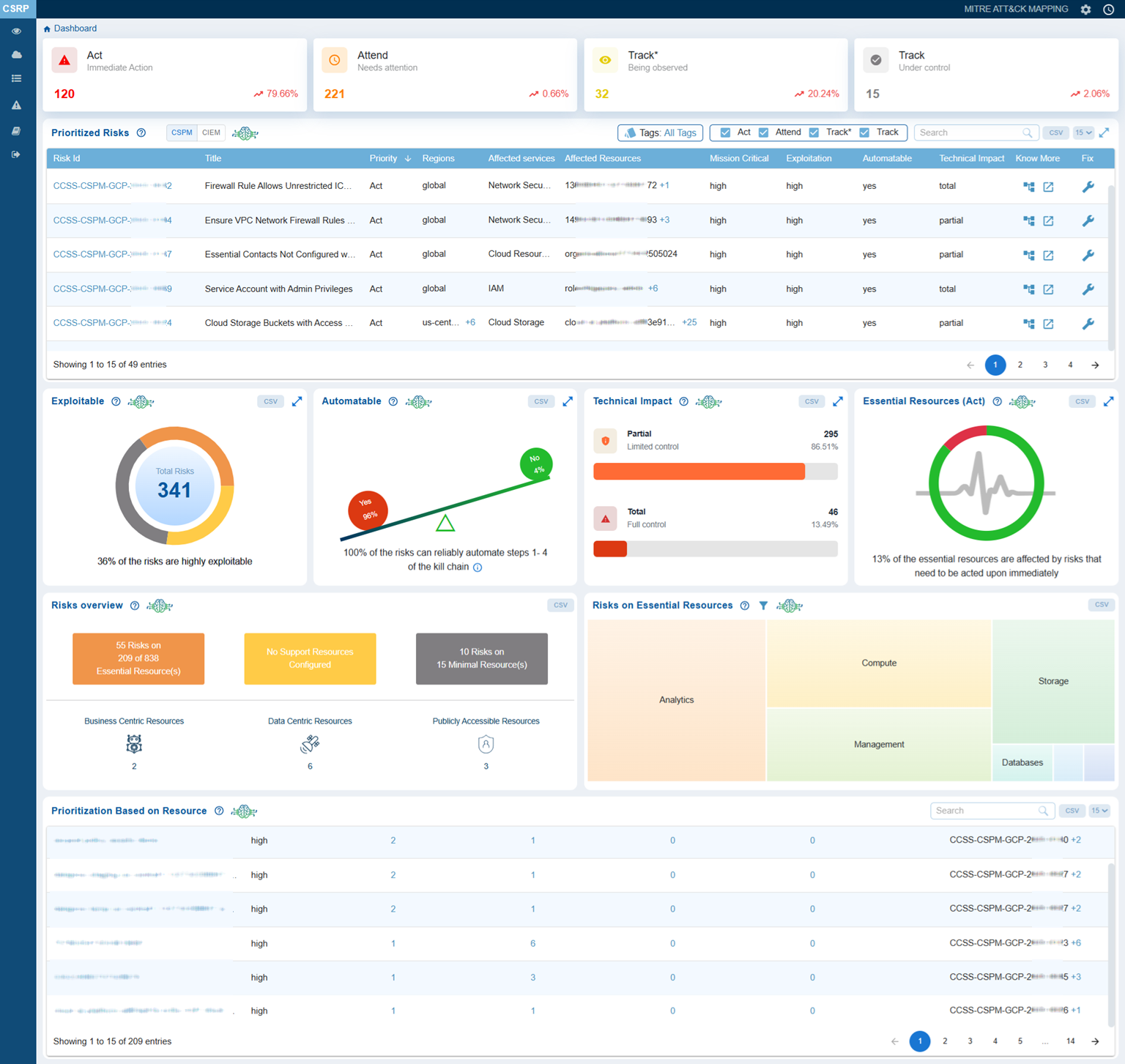
GCP Risk Findings Integrated into Cloud Security Risk Prioritization
Saner Cloud Security Risk Prioritization (CSRP) actively ingests and prioritizes security findings across your Google Cloud environment, allowing teams to remediate the most critical risks faster.
The platform delivers a unified, risk-driven view across GCP organizations and projects, analyzing risks associated with assets such as Compute Engine instances, Cloud Storage buckets, IAM roles, VPC networks, and BigQuery datasets for exploitability, technical impact, and mission relevance.
Using a stakeholder-specific vulnerability categorization (SSVC) model, CSRP classifies GCP risks into clear, actionable decisions such as Act, Attend, Track*, and Track, so the right teams respond with the right urgency. By mapping findings to MITRE ATT&CK techniques, CSRP provides real-world attack context and empowers organizations to reduce cloud risk with confidence.
Staying Updated on GCP Hygiene Score with Cloud Cyber Hygiene Score (CCHS)
Saner Cloud Cyber Hygiene Score (CCHS) quantifies risks by aggregating misconfigurations, identity exposures and other security findings into a measurable Raw Score that reflects overall cloud risk. It quantifies this data into Global and Local Scores to benchmark security posture against industry standards and internal environments. CCHS continuously updates these scores to provide real-time visibility into changes in risk levels.
When teams remediate issues such as excessive permissions or insecure configurations, the score improves, clearly demonstrating reduced exposure. This measurable improvement proves the value of proactive prevention by showing tangible, trackable risk reduction across the GCP environment.

Unified Multi-Cloud Security Visibility
The unified multi-cloud view helps your organization manage and monitor cloud security across GCP, AWS, and Azure through a centralized dashboard, improving visibility and simplifying multi-cloud governance.
The dashboard brings AWS, Azure, and GCP into a single, consistent security view, eliminating the need to switch between multiple cloud consoles. Instead of managing siloed tools and fragmented reports, security teams gain centralized visibility across assets, risks, compliance status, anomalies, entitlements, and recommended remediation patches available in one place.



