The Container Orchestration Security Platform (COSP) provides a comprehensive framework to help organizations secure, monitor, and manage their containerized environments, particularly those powered by Kubernetes. As the adoption of containers increases, ensuring visibility, control, and security across clusters becomes vital. This guide explains how Saner COSP simplifies these responsibilities through an integrated, end-to-end approach.
At its core, the platform allows you to secure and manage Kubernetes clusters by offering deep insights into how clusters, nodes, and workloads operate. It begins by helping you understand the role of clusters in container orchestration, forming the foundation for efficiently and securely managing distributed applications.
The guide introduces Container Orchestration Asset Exposure (COAE) tool that helps you identify publicly exposed assets, misconfigured resources, and potential attack surfaces within your cluster environment. Building on this, Container Orchestration Posture Management (COPM) enables you to identify compliance gaps against security benchmarks and best practices, ensuring that your configurations align with both organizational and industry standards. To further enhance security, the Container Orchestration Entitlement Management (COEM) tool allows organizations to systematically identify excessive permissions across various identities, including Kubernetes users, groups, service accounts, roles, and cluster roles, making sure that access rights align with the Principle of Least Privilege. In addition, Container Orchestration Posture Anomaly (COPA) helps you detect unusual configurations and anomalies, enabling faster investigation and mitigation of potential risks. The guide also discusses Container Orchestration Remediation Management (CORM), which allows you to monitor remediation activities and track patch deployments. This ensures that identified issues are resolved efficiently and consistently. Finally, Saner COSP supports report generation and visualization that help track security posture, remediation progress, and overall cluster health.
Together, these capabilities offer a unified approach to container security, compliance, entitlement management, anomaly detection, and remediation, empowering teams to maintain a strong and proactive security posture across their container orchestration environments.
Secure and Manage Your Kubernetes Clusters with Saner COSP
Kubernetes organizes and manages a deployment through automation and uses the Clusters, Nodes, Pods, and Kubernetes API as the building blocks. Saner COSP engages with Kubernetes cluster to simplify container security management tasks that include finding assets that are exposed to the internet, misconfigurations in various resources that are running, anomalies in how the cluster is setup, entitlement management. Saner COSP also enables remediating these issues easily through a few clicks and setting up sophisticated remediation rules.
Understand the Role of Clusters in Container Orchestration
By using clusters as the foundation of Container Orchestration, Kubernetes logically separate sparts of your infrastructure and application from each other, making it easier to visualize your business.
Inside a Kubernetes Cluster

The Kubernetes cluster simplifies the management of multiple scalable applications by separating it into different Deployments. These deployments include Images and other necessary components required to make an application available. The Images view helps maintain image hygiene by identifying outdated or vulnerable container images, while the Containers view provides a detailed breakdown of active containers to make sure they operate securely and adhere to runtime policies. The cluster also features Namespaces, allowing administrators to manage resource segmentation and isolate compliance or security issues within specific environments. Kubernetes manages the allocation of application instances into Nodes as desired. By relying on Services that practically acts as a static endpoint and a load balancer, the administrator can ensure that applications can scale up and down in the Kubernetes cluster flawlessly.
Saner COSP dashboard provides a centralized and visual representation of the Kubernetes environment, summarizing the operational and security posture of each component, helping teams quickly assess operational health, identify risks, and prioritize remediation across Deployments, Images, Namespaces, Nodes, and Services.
Manage Control Plane Nodes in a Cluster
Control-plane nodes, also known as master nodes, are the central components of a Kubernetes cluster. They are responsible for managing the overall state and operations of the cluster. These nodes perform critical functions, including scheduling containers onto worker nodes, monitoring the health of the cluster, and making sure that the actual state of the cluster matches the desired state. Additionally, control-plane nodes expose the cluster API, which tools like kubectl use to interact with and manage workloads.
The key components of the “Control Plane” nodes include:
- kube-apiserver: The API interface for users and tools to interact with the cluster.
- etcd: A key-value store that holds the configuration and state of the cluster.
- kube-scheduler: Responsible for determining where containers should be run within the cluster.
- controller-manager: Oversees deployments, replica sets, and other controllers to ensure the desired state is maintained.
In Saner Cloud COSP dashboard, Control Plane Nodes provides a real-time count of all control plane nodes currently running workloads. Displaying the control plane nodes count on the dashboard helps administrators monitor the stability and reliability of cluster management operations. The control plane nodes host key components such as the API server, controller manager, scheduler, and etcd , all essential for maintaining cluster state and orchestrating workloads. Tracking their count ensures that the control plane is properly replicated and highly available. A reduced or unstable control plane node count may signal configuration issues, failures, or risks to cluster availability. By monitoring this metric, administrators can quickly identify and address problems that could affect the overall orchestration, scheduling, and decision-making processes within the Kubernetes cluster.
Manage Worker Nodes in a Cluster
Worker nodes are the machines where Kubernetes runs your applications. They execute containers organized into pods and communicate with the control-plane nodes to maintain the health and availability of workloads. Each worker node provides essential resources, such as CPU, memory, storage, and networking, that containers need to function properly.
The key components of the “Worker” nodes include:
- kubelet: An agent that communicates with the control plane and ensures that containers are running as expected.
- Container runtime: The engine responsible for running containers (e.g., Docker, containerd).
- kube-proxy: Manages networking to ensure that pods can communicate with each other and with external services.
In Saner Cloud COSP dashboard, Worker Nodes provides a real-time count of all worker nodes currently running workloads. Displaying the worker nodes count on the dashboard helps administrators quickly assess the cluster’s operational capacity and health. It provides an overview of how many nodes are currently active and available to run workloads, which is crucial for resource planning, load distribution, and fault tolerance. A sudden drop in node count can indicate node failures, connectivity issues, or autoscaling problems, prompting immediate investigation. Monitoring node count also helps ensure workloads are properly balanced across the cluster and that there are sufficient resources to handle current and future deployment demands.
Monitor and Manage Active Namespaces in Kubernetes
In Kubernetes Container Orchestration, namespaces act as logical partitions within a cluster. They allow teams to organize, isolate, and manage resources such as pods, services, and configurations independently. Namespaces help enforce security boundaries, implement role-based access controls (RBAC), and define resource quotas for improved governance.
Active namespaces are those that currently host running workloads or demonstrate operational activity, such as ongoing deployments, updates, or monitoring metrics. Together, namespaces and active namespaces facilitate efficient resource organization, workload isolation, and targeted policy enforcement, ensuring scalable, secure, and well-managed containerized environments.
In Saner Cloud COSP dashboard, Active Namespaces provides a real-time count of all namespaces currently running workloads. This helps administrators quickly assess activity levels, detect potential issues, and maintain optimal cluster performance and compliance.
Monitor Images
In Kubernetes Container Orchestration, a container image is an executable software package that includes everything necessary to run an application, such as the code, runtime, libraries, dependencies, and configuration files.
Saner Cloud COSP displays the Image count, helping administrators maintain visibility and control over the container ecosystem. A high or rapidly increasing image count may indicate the presence of redundant or outdated images, which can lead to misconfigurations and inefficient resource usage. Monitoring this metric enables administrators to identify unapproved or unscanned images, enforce standardization of base images, and ensure that only trusted, up-to-date versions are in use.
Clicking on the image count from the dashboard block, navigates you to the All Images details page providing information on the Image ID, Image Name, Namespace, Container ID, Container Name, and Pod Name.
Monitor Containers
In Kubernetes Container Orchestration, containers are the smallest deployable units that package and run application workloads. Each container is created from a container image, which includes the application code, runtime, libraries, and all necessary dependencies needed to ensure the application runs consistently across different environments.
The Saner Cloud COSP dashboard displays the container count, helping administrators assess workload density, resource utilization, and the overall health of the cluster. It shows the number of containers that are currently running, pending, or failed across namespaces and nodes, providing a clear snapshot of cluster activity. Monitoring the container count allows for the detection of unusual spikes or drops, which may indicate scaling events, deployment issues, or resource bottlenecks. Additionally, it helps monitor workload distribution, ensuring that containers are efficiently scheduled across nodes and namespaces. From a compliance and security perspective, tracking the container count validates that only authorized containers are active. Overall, this metric supports capacity planning, performance monitoring, and anomaly detection within Kubernetes environments.
Identify Exposure with Container Orchestration Asset Exposure(COAE)
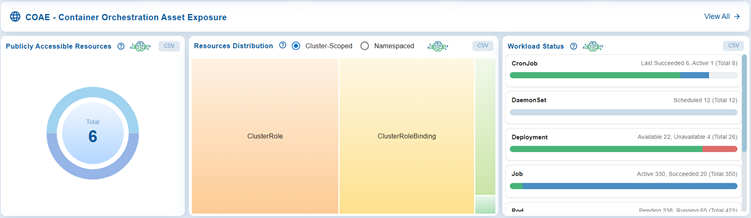
The COAE(Container Orchestration Orchestration Asset Exposure) view focuses on identifying exposed assets within the Kubernetes environment. It highlights open port distribution across workloads, differentiates between cluster-scoped and namespaced resources, and provides the status of workloads for example, Deployments, StatefulSets, DaemonSets, CronJobs and so on.
The objective is to minimize the cluster’s attack surface by tracking exposure levels and workload health.
Click the View All button on the top-right corner of the COAE – Container Orchestration Orchestration Asset Exposure dashboard view toaccess all the security insights gathered about exposure.
Follow the link for detailed information on working with the different dashboard views in COAE.
Identify Configuration Gaps in Compliance Posture with COPM
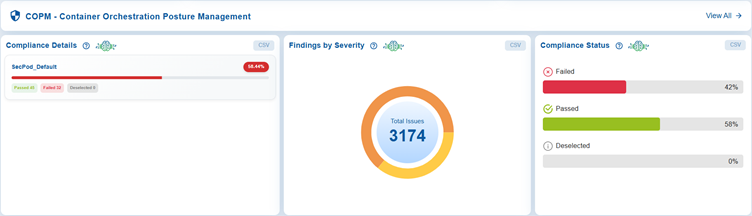
The COPM(Container Orchestration Posture Management) view ensures compliance with established security framework and policies. It presents the SecPod Default compliance scores(expressed in percent) and maps them against standards like CIS, NIST, PCI DSS, and HIPAA, and categorizes issues by severity. It also tracks compliance status to show which checks have passed, failed, or remain unchecked.
The objective is to continuously strengthen security posture by identifying and remediating configuration gaps.
Click the View All button on the top-right corner of the COPM – Container Orchestration Posture Management dashboard view toaccess the details on deviations from compliance standards and appropriate remediations that can be triggered conveniently.
.
Control and Optimize Access Permissions
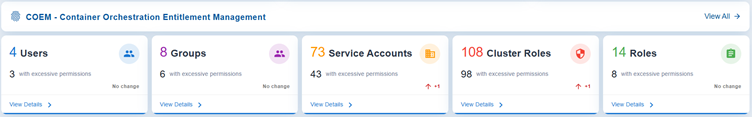
The Container Orchestration Entitlement Management(COEM) detects and manages excessive permissions across different identities and roles in the cluster. It highlights risks associated with users, groups, service accounts, cluster roles, and roles with permissions beyond necessity. Risks are classified as high, medium, or low. The objective is to enforce least-privilege principles and reduce the likelihood of insider threats or privilege escalation.
Each block highlights where excessive permissions are concentrated, so administrators can prioritize remediation. The dashboard’s enforces the principle of least privilege across users, groups, service accounts, and roles at both cluster and namespace levels.
Users
Track individual accounts and make sure the user accounts only have the permissions necessary for their role. This view also helps prevent privilege creep where users accumulate unnecessary rights over time.
The Users section lists all individual accounts with access to the environment and highlights those with excessive permissions.
Groups
The Groups view helps manage collections of users with shared permissions. By making sure that group-level access is properly scoped you can avoid configured groups that unintentionally grants broad access to many users at once.
Groups provide a summary of all configured access groups and highlights those with permissions that exceed operational requirements.
Service Accounts
Service Accounts focus on accounts used by applications or automated services with the goal to keep these accounts tightly controlled, since they often run continuously and can be exploited if over‑privileged. It highlights service accounts with elevated privileges, which are frequently overlooked but present significant security risks if compromised.
Cluster Roles
Govern permissions that apply across the entire cluster, so the focus is on reducing excessive rights to minimize cluster-wide security risks.
Cluster Roles provide insights into access policies at the cluster level that affect multiple namespaces or services. It emphasizes roles with extensive or administrative permissions, allowing administrators to evaluate and improve security boundaries across the cluster.
Roles
Defines permissions at the namespace level to ensure fine-grained access control within specific environments, preventing unnecessary escalation of privileges beyond what’s needed locally.
Roles address access roles specific to namespaces or projects. It aids in identifying localized roles with excessive privileges, allowing for precise control over permissions and ensuring strong internal access segregation.
Detect and Investigate Security Anomalies with COPA
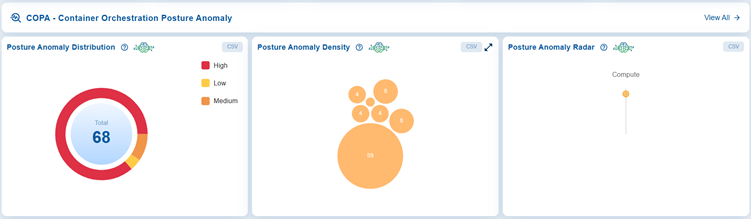
The COPA dashboard offers a centralized view of posture anomalies in Container Orchestration environments, helping administrators quickly identify and prioritize risks. In this case, the dashboard block displays a total of 68 anomalies, categorized by severity levels (high, medium, and low) using a circular chart. Additionally, it highlights anomaly density through a bubble chart, where the largest cluster consists of 59 issues. The dashboard also identifies affected categories with a radar visualization, which currently shows that anomalies are concentrated in the “Compute” area. Together, these features provide a clear overview of system health, enabling proactive monitoring and remediation of security posture issues.
Click the View All button on the top-right corner of the COPA – Container Orchestration Posture Anomaly dashboard view toaccess the overall cloud orchestration posture anomaly dashboard.
Follow the link for detailed information on working with the different dashboard views in COPA.
Monitor Remediation Progress, Patch Distribution, and Workflow Status with CORM
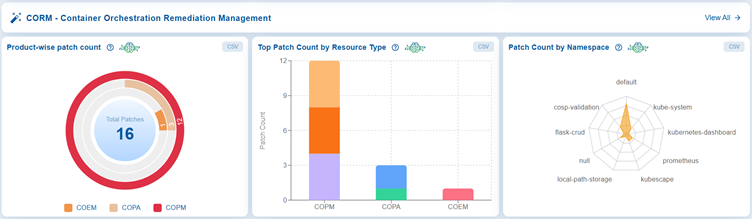
The Container Orchestration Remediation Management(CORM) view provides a remediation summary, including available and automated fixes, rollbacks, and patch counts, along with workflow status across completed, failed, and pending tasks. The objective is to streamline and automate remediation efforts, ensuring timely resolution of vulnerabilities and misconfigurations.
Click the View All button on the top-right corner of the CORM – Container Orchestration Remediation Management dashboard view to access all available remediation to secure you cluster and achieve compliance.
Follow the link for detailed information on working with the different dashboard views in CORM.
Generate Reports and Visualizations
Access COSP Reports
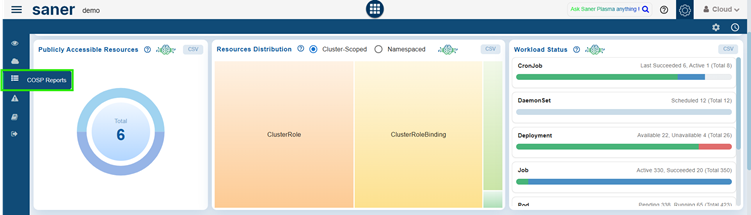
From the side bar, click on the COSP Alerts menu.
Create Custom Report Views
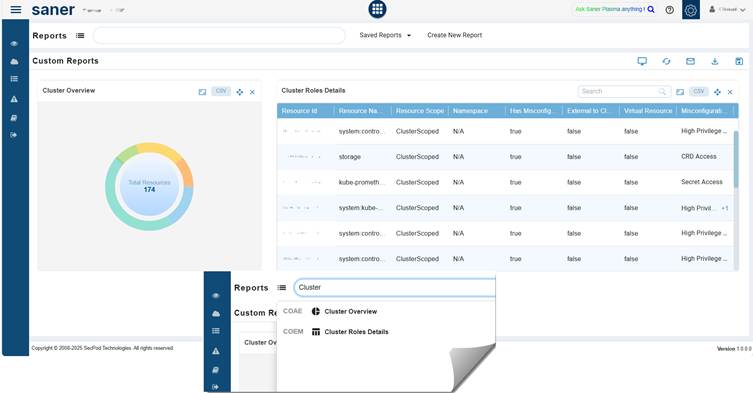
Just go ahead and key in the report name within the Report APIs textbox. The system extracts the report from the Cloud Infra dashboard and embeds in the Custom Reports section.
View Based on Cluster Overview and Cluster Role Details
Cluster Overview provides the big picture of resource distribution and drills down into specific roles, highlighting misconfigurations and privilege levels that could pose security risks.
Cluster Roles Details drills down into specific roles, highlighting misconfigurations and privilege levels that could pose security risks. This report provides a detailed tabular view of cluster roles and their configurations.
Column details as follows:
- Resource ID: Unique identifier for the role
- Resource Name: Name of the resource
- Resource Scope: Indicates if the role is ClusterScoped or namespace-specific
- Namespace: Shows the namespace (N/A for cluster-scoped roles)
- Has Misconfig: Boolean flag indicating misconfiguration presence
- External ID: Identifies external linkage if any
- Virtual Resource: Marks if the resource is virtual
- Misconfiguration: Describes the type of issue (for example, High Privilege, CRD Access, Secret Access)


